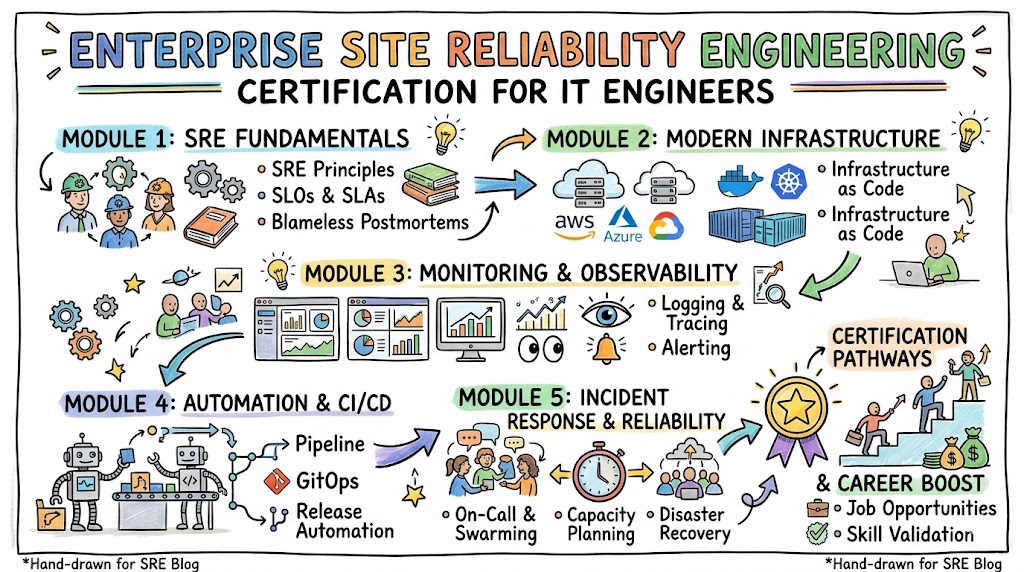
Enterprise Site Reliability Engineering Certification for IT Engineers
Introduction Modern enterprise infrastructure requires robust systems that can handle scale, velocity, and unpredictable failure modes. The Certified Site Reliability Engineer program bridges the gap between traditional software development and IT operations by instilling a production-first mindset. This comprehensive guide is designed for engineering professionals, infrastructure specialists, and engineering managers who want to validate their … Read more